コンプリート! is-is protocol 256530-Is-is protocol number
Protocol is a rules definition of how things should work Its a set of rules that as a developer you can code your application too and as long as you follow the rules of the protocols your application can talk successfully to other applic What is a protocol?Answer (1 of 5) Q What is the importance of protocols?
Why Do Many Isps Still Use The Is Is Instead Of The Ospf
Is-is protocol number
Is-is protocol number-How can it be used in an authentication protocol?Polychain Protocol is excited to announce our product advisor and partnership with Peech Capital Peech Capital is an investment and advisory firm that focus on early stage DeFi and blockchain projects The experience and knowledge the Peech Capital team possesses is a valued addition to our already experienced team



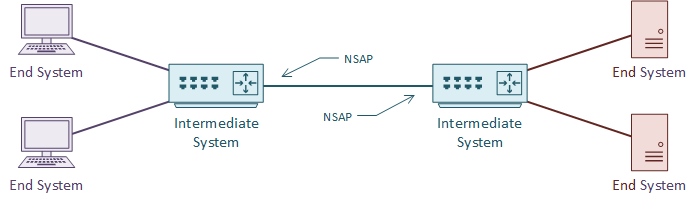
Intermediate System Intermediate System Is Is Protocol Octa Networks
A CT protocol is a set of parameters that specify a specific exam and contrast delivery requirements When a CT scan is requested, it will be vetted by a radiologist or radiographer to determine the study is justified and what the most suitable parameters by which that CT should be performed this may lead to a different CT examination being performed or an alternativeYou cannot use itWhat is a protocol?Protocols are how networked computers communicate But unlike human speech, computer communication has to be highly structured and extreme
Human protocol (or good manners ,at least) dictates that one first offer a greeting (the first "Hi") to initiate communication with someone else The typical response to a "Hi" is a returned "Hi" message Implicitly, one then takes a cordial "Hi" response as an indication that one can proceed and ask for the time of day A protocol is a set of rules and guidelines for communicating data Rules are defined for each step and process during communication between two or more computers Networks have to follow these rules to successfully transmit data AdvertisementARP (Address Resolution Protocol) is a network protocol used to find out the hardware (MAC) address of a device from an IP address It is used when a device wants to communicate with some other device on a local network (for example on an Ethernet network that requires physical addresses to be known before sending packets)
"A few hours ago, Proposal 62 went into effect, updating the Comptroller contract, which distributes COMP to users of the protocol The new Comptroller contract contains a bug, causing some users to receive far too much COMP" Leshner says that all the crypto assets locked on the DeFi platform's smart contracts are safe What is CSMA protocol?The Internet Protocol (IP) is a protocol, or set of rules, for routing and addressing packets of data so that they can travel across networks and arrive at the correct destination Data traversing the Internet is divided into smaller pieces, called packets IP information is attached to each packet, and this information helps routers to send




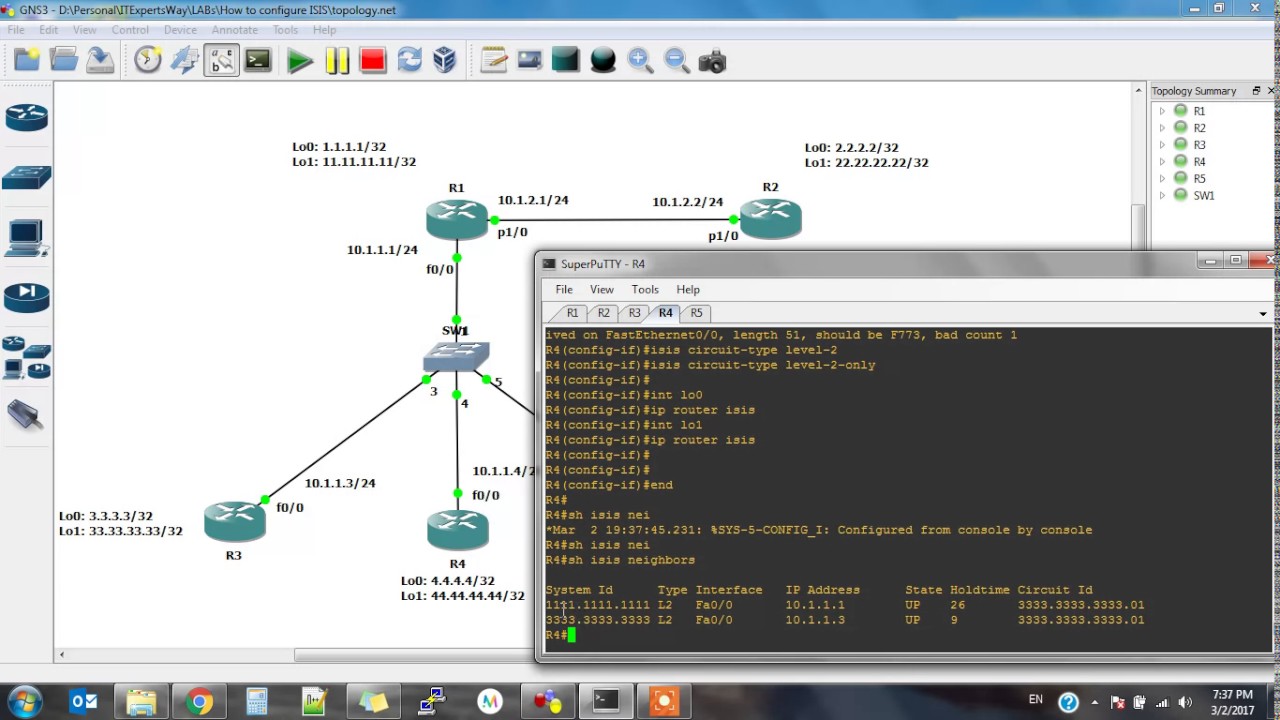
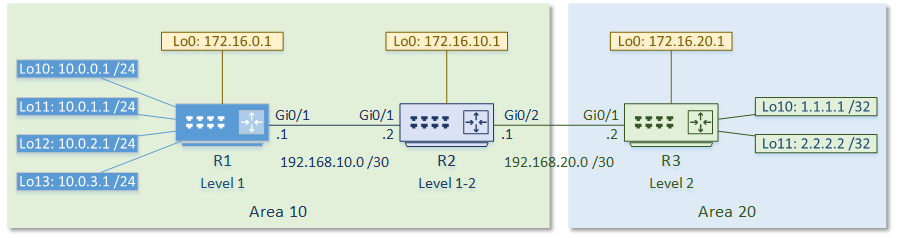
Basic Integrated Is Is Router Configuration Configuring Is Is Protocol Cisco Press




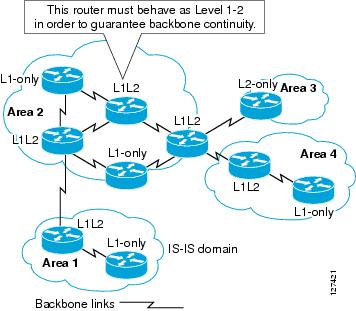
Is Is Route Leaking Overview Cisco
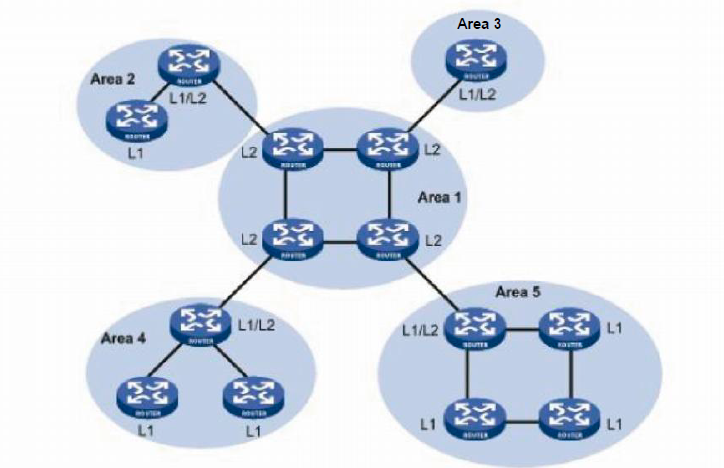
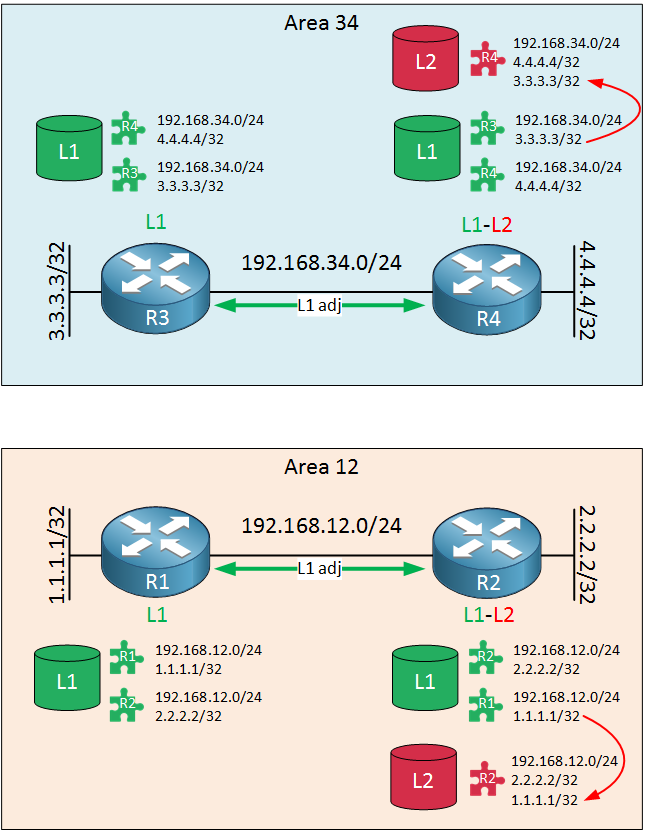
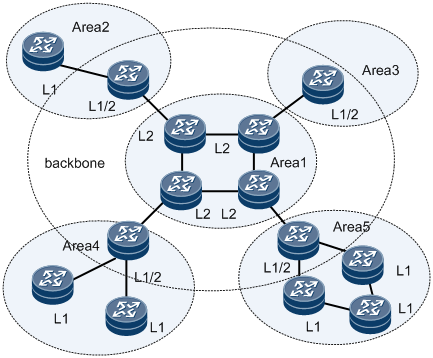
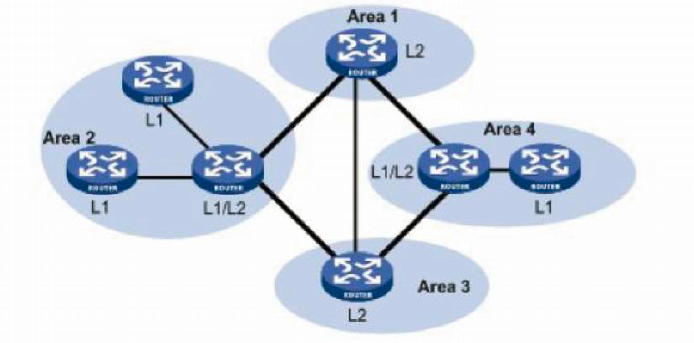
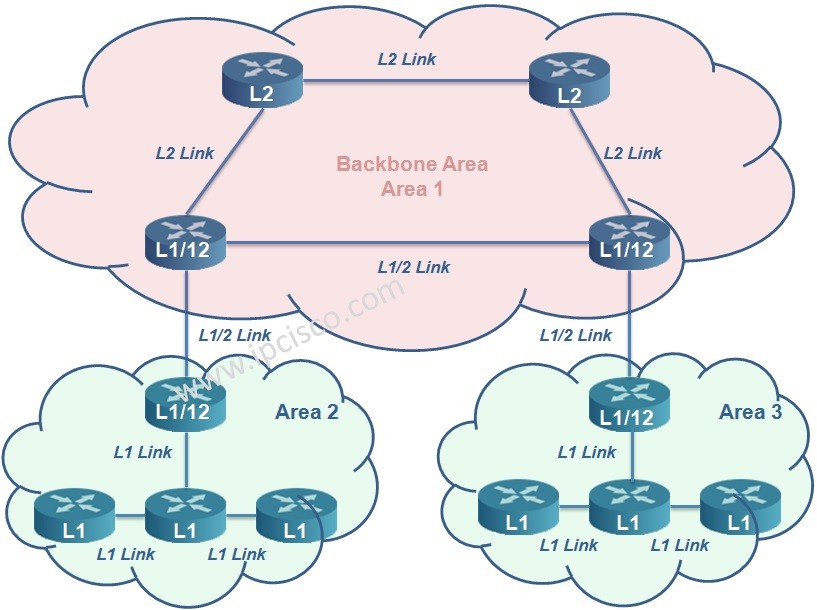
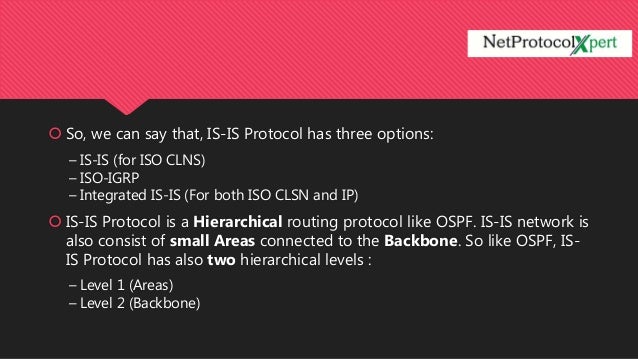
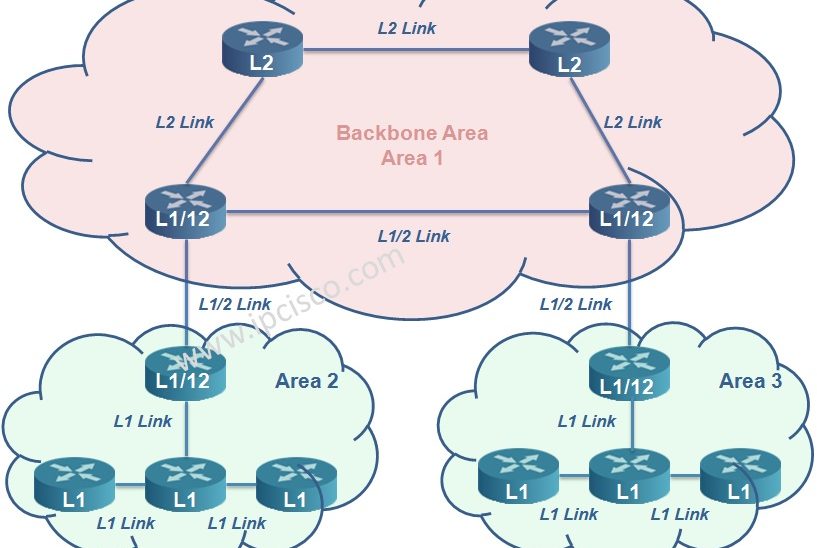
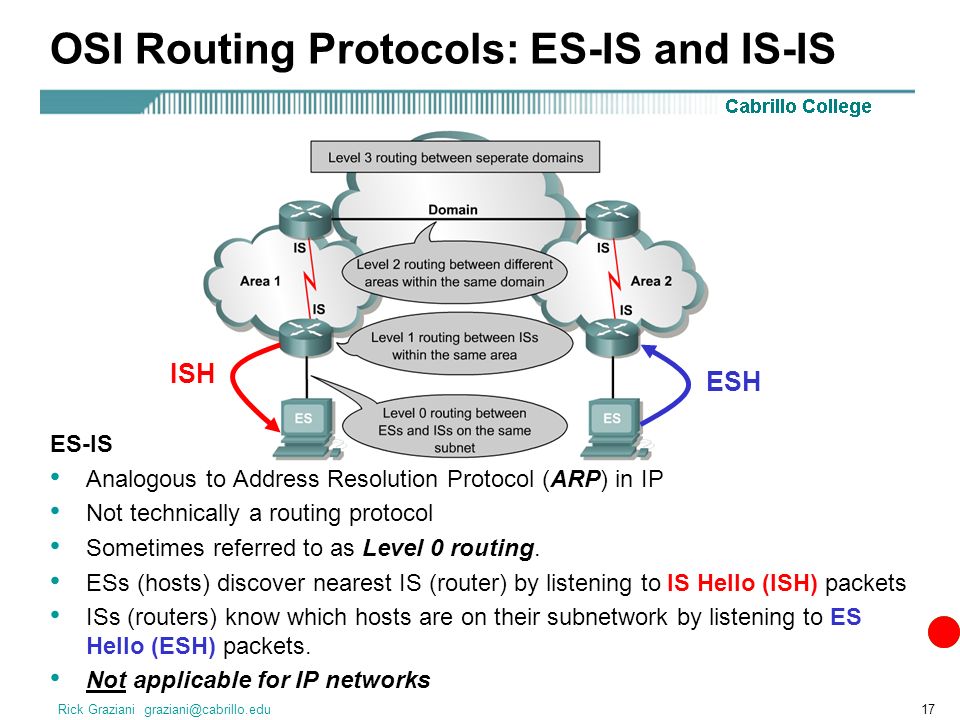
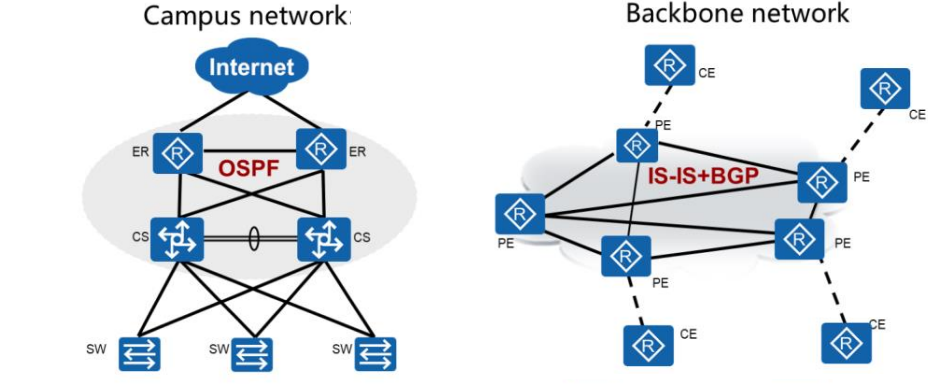
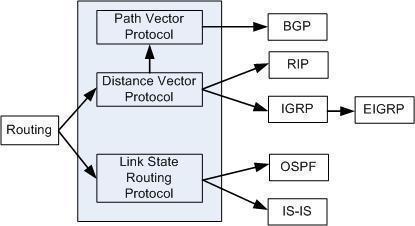
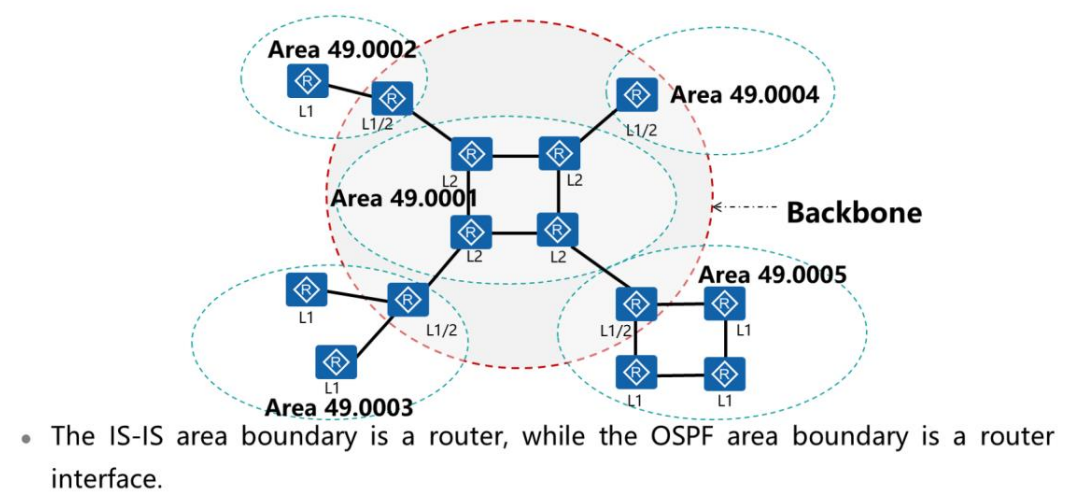
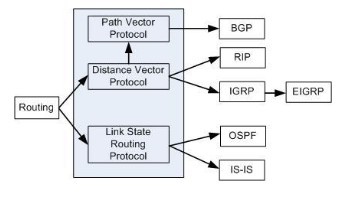
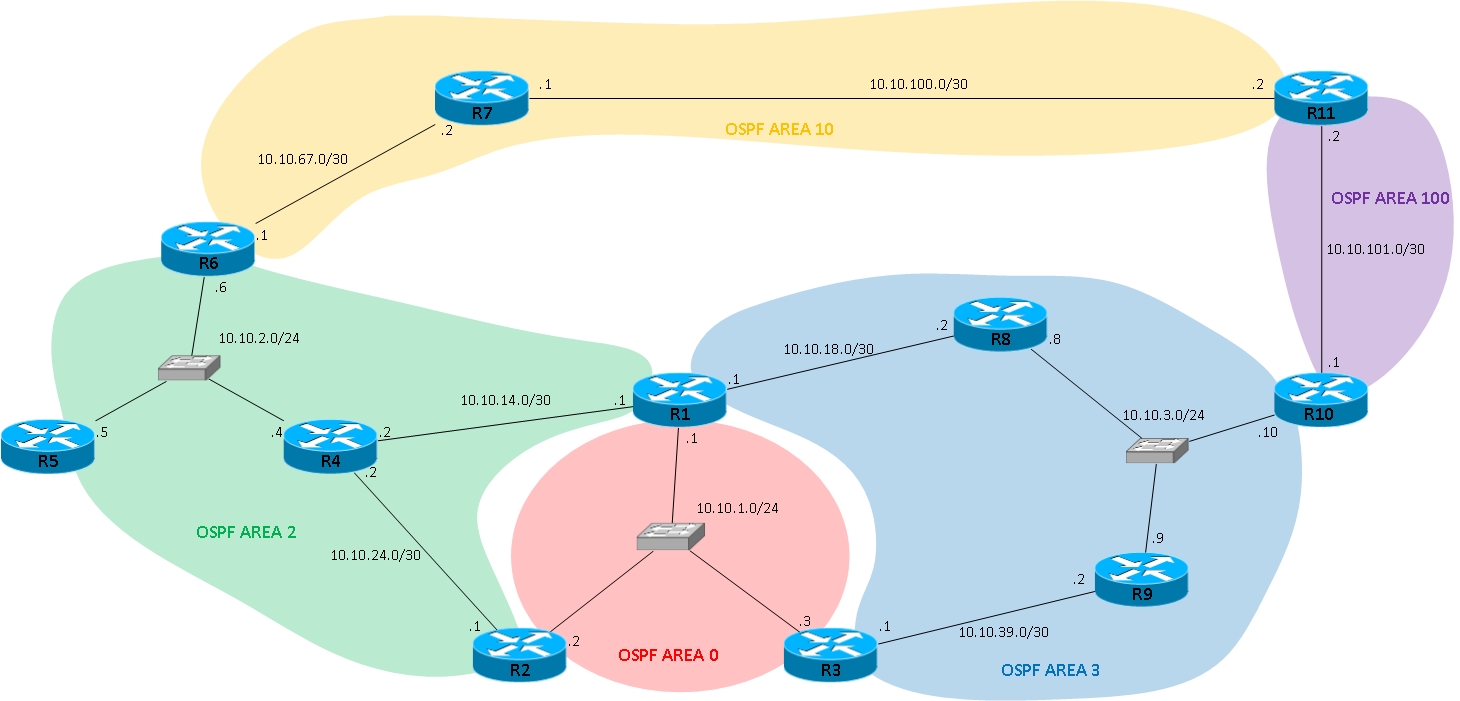
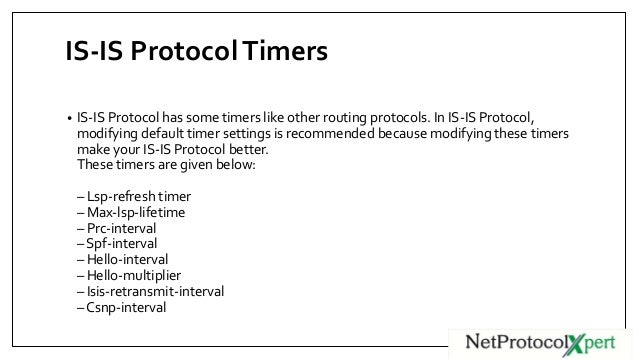
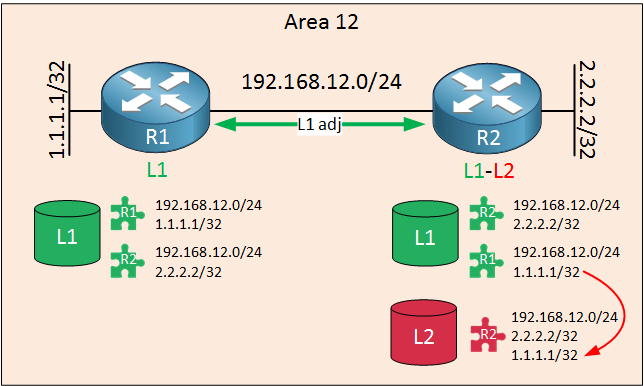
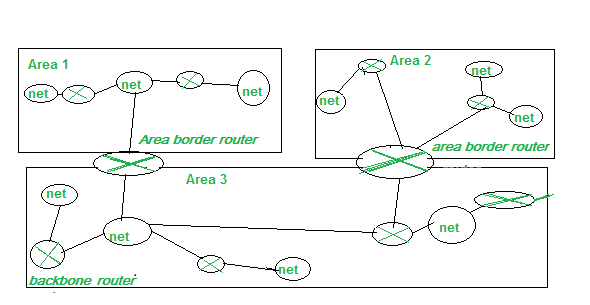
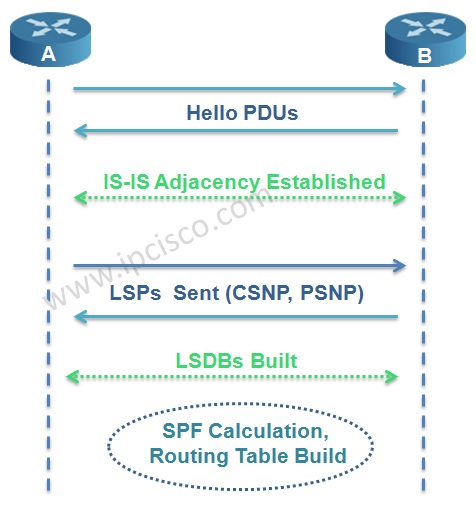
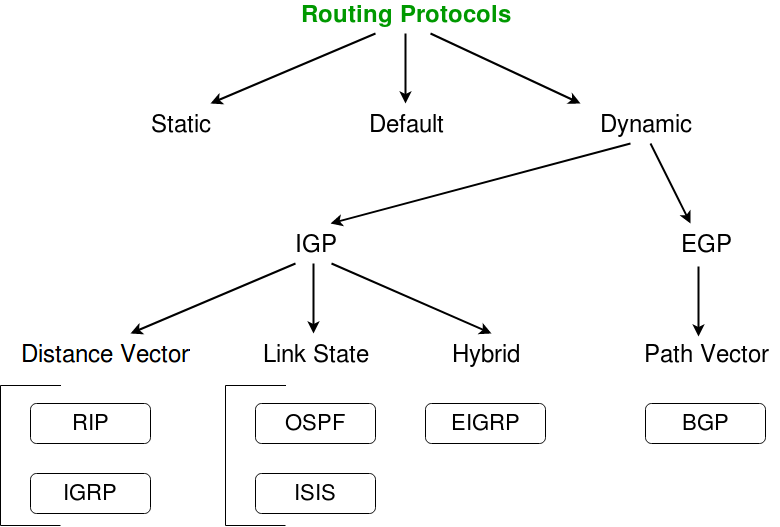
A protocol is registered to a specific Electron session object If you don't specify a session, then your protocol will be applied to the default session that Electron uses However, if you define a partition or session on your browserWindow 's webPreferences, then that window will use a different session and your custom protocol will not workThe protocol is called Transport Layer Security (TLS), although formerly it was known as Secure Sockets Layer (SSL) This protocol secures communications by using what's known as an asymmetric public key infrastructure This type of security system uses two different keys to encrypt communications between two partiesISIS Overview The ISIS protocol is an interior gateway protocol (IGP) that uses linkstate information to make routing decisions ISIS is a linkstate IGP that uses the shortestpathfirst (SPF) algorithm to determine routes



Introduction To Is Is




Integrated Is Is Routing Protocol Training With Cisco Ios Advanced 3 Clip1 Youtube
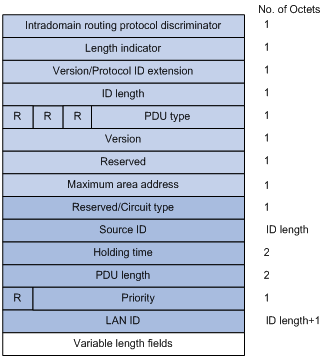
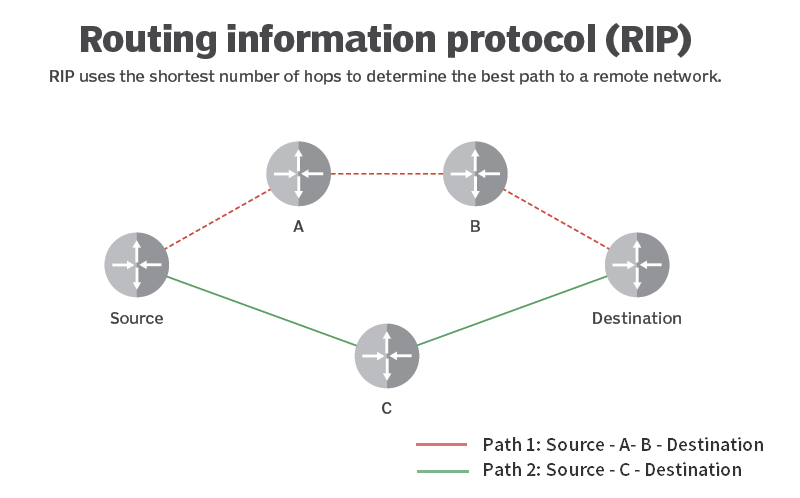
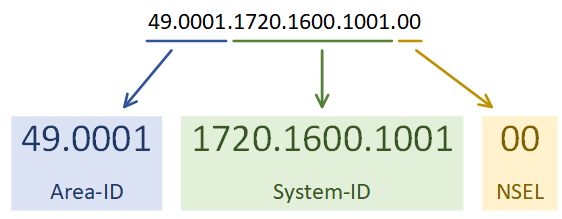
ISIS is an extendible intradomain routing protocol Each router in the routing domain issues an Link State Protocol Data Unit (LSP) that contains information pertaining to that router The LSP contains typed variablelength data, often referred to as TLVs (typelengthvalues)It is a simple protocol so it is one of the most popular protocols used today It is easy to configure and use Disadvantages of POP3 protocol The following are the advantages of a POP3 protocol If the emails are downloaded from the server, then all the mails are deleted from the server by defaultProtocol meaning 1 the system of rules and acceptable behaviour used at official ceremonies and occasions 2 a Learn more



Is Is Pdu Format



Integrated Is Is Basics Amolak Networks
Also, the precise method for carrying out or reproducing a given experimentNetwork protocol A network protocol is a set of established rules that dictate how to format, transmit and receive data so that computer network devices from servers and routers to endpoints can communicate, regardless of the differences in their underlying infrastructures, designs or standards HTTP (Hypertext Transfer Protocol) is the fundamental protocol used for transferring files on the internet This definition explains how HTTP the request and response process between client and server, as well as the differences between HTTP and HTTPS and common response status codes



3




Is Is Packets Integrated Is Is Routing Protocol Concepts Cisco Press
Define protocol protocol synonyms, protocol pronunciation, protocol translation, English dictionary definition of protocol n 1 a The forms of ceremony and etiquette observed by diplomats and heads of state b A code of correct conduct safety protocols;The protocol of the bull contains elements that appear to be formulaic by the time of John XVIII 's pontificate (sciences) The original notes of observations made during an experiment;As a requestresponse protocol, HTTP gives users a way to interact with web resources such as HTML files by transmitting hypertext messages between clients and servers HTTP clients generally use Transmission Control Protocol (TCP) connections to



Isis As Sbi Onos Wiki



Intermediate System Intermediate System Is Is Protocol Octa Networks
Protocol definition is an original draft, minute, or record of a document or transaction How to use protocol in a sentence protocol and Politics HTTP, or hypertext transfer protocol, is the entire backbone of the world wide web It is the protocol used to process, render, and deliver web pages from the serverside to the client browser HTTP is the means through which most of the web is displayed HTTP and HTTPS work through what are called requestsIt is a protocol for securing the communication between two systems eg the browser and the web server The following figure illustrates the difference between communication over http and https Communication over https and http As you can see in the above figure, http



Is Is Ipcisco



Is Is Protocol Introduction
This is a list of the IP protocol numbers found in the field Protocol of the IPv4 header and the Next Header field of the IPv6 headerIt is an identifier for the encapsulated protocol and determines the layout of the data that immediately follows the header DDavid Frost, Minister responsible for relations with Brussels, used the Conservative Congress to make threats against the European Union to tighten In a speech to the delegates in Manchester on Monday, he said that Great Britain would suspend the socalled Northern Ireland Protocol in the exit treaty if the ongoing negotiations with the EU CommissionProtocol Definition The term protocol encompasses several meanings, while the most frequent and frequent use by the ordinary people refers to the set of behaviors and rules that a person must observe and respect when moving in specific official fields either for a matter of unique circumstance or because it holds a position that leads to transit through them



Isis Training And Junos Configuration Inetzero Inetzero



Is Is Link State Packets Is Is Network Design Solutions Networking Technology
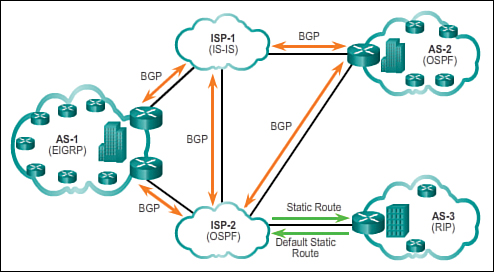
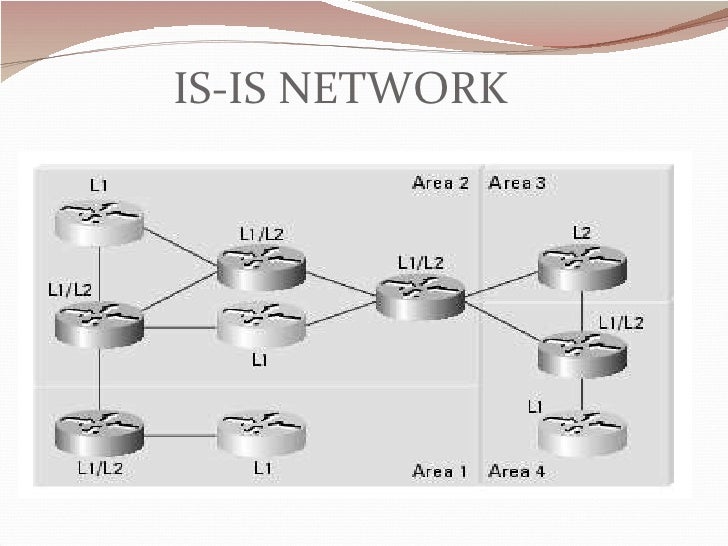
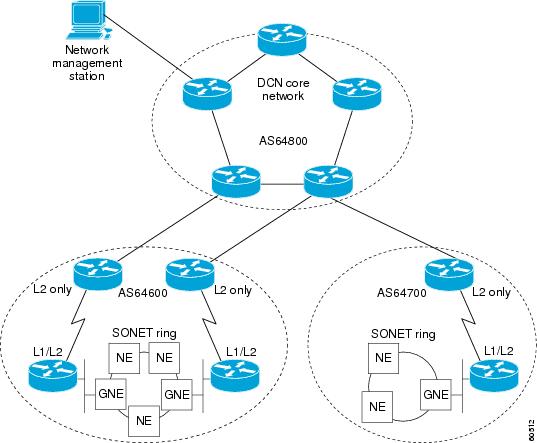
It is a one time only number or a "numberonlyonce" In authentication schemse, it prevents replay attacks because when attached to a message, it marks that message as being only valid for that one time;The ISIS (Intermediate System Intermediate System) protocol is one of a family of IP Routing protocols, and is an Interior Gateway Protocol (IGP) for the Internet, used to distribute IP routing information throughout a single Autonomous System (AS) in an IP network ISIS is a linkstate routing protocol, which means that the routers NEAR Protocol is a blockchain that operates on a Public Proof of Stake and Sharded (shard) mechanism It is like a community run, highly scalable and low cost cloud platform for developers to create decentralized applications easily NEAR is secure enough to manage highvalue assets like money or identities and efficient enough to make them




The Aerodynamics Of Routing Ciena




Is Is Overview And Lab Ccie
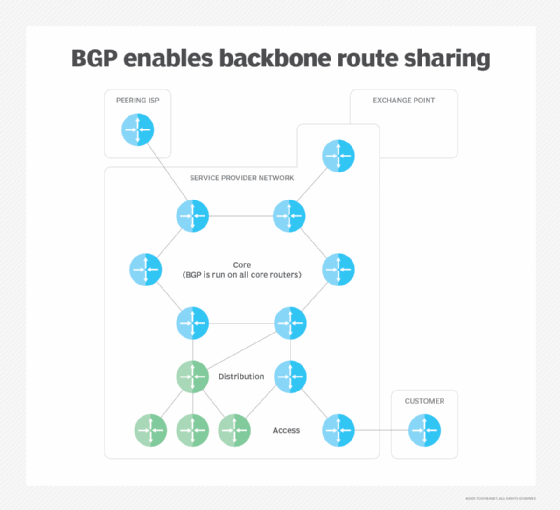
Genie Protocol Decentralized Finance made simple!Border Gateway Protocol (BGP) is a standardized exterior gateway protocol designed to exchange routing and reachability information among autonomous systems (AS) on the Internet BGP is classified as a pathvector routing protocol, and it makes routing decisions based on paths, network policies, or rulesets configured by a network administrator BGP used for routing withinA protocol is a system of rules that define how data is exchanged within or between computers Communications between devices require that the devices agree on the format of the data that is being exchanged The set of rules that defines a format is called a protocol




The Isis Link State Pdu Format Routing Tcp Ip



Is Is Protocol Introduction
The Protocol IT services (Protocol IT IS Services Pty Ltd) is a Canning Vale, South of the river Perth, Western Australian based company that strives to provide results orientated consultancy that delivers innovative technologybased solutions to manage your business and corporate IT needsThe Factom protocol was designed from the start for sharding The Factom protocol is pure data Separating token transactions and computation from the data layer allows for efficient sharding of the blockchain An efficiently sharded data blockchain allows for continuous and real time securing of the level of data enterprise customers demandCarriersense multiple access (CSMA) is a media access control (MAC) protocol in which a node verifies the absence of other traffic before transmitting on a shared transmission medium, such as an electrical bus or a band of the electromagnetic spectrum



Is Is Protocol Archives Ipcisco




Isis Protocol Overview Youtube
Buy and sell dozens of tokens that you like at once and earn money from the fees that the Genie Protocol generates, quickly and easily Buy GNP Prove to be a true hodler and receive a rich reward in GNP tokensIf you arrived here, this probably means that you have heard before of something called protocol The first thing to know is that there are a bunch of protocols, not only one, and that every protocol has a bunch of rules inside him ISSUAA is a decentralized finance protocol designed to tokenize realworld and crypto assets like indices, stocks, commodities, cryptocurrencies, etc, on the public blockchain In other words, ISSUAA Protocol enables the creation, minting, and development of synthetic assets that reflect the price of underlying realworld and crypto assets



How To Configure Isis Protocol Step By Step Youtube



Introduction To Is Is
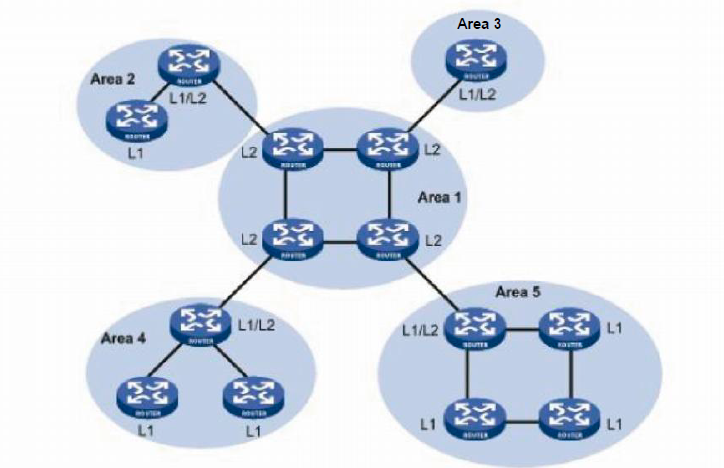
ISIS is a linkstate interior gateway routing protocol Like OSPF, ISIS runs the Dijkstra shortestpath first (SPF) algorithm to create a database of the network's topology and, from that database, to determine the best (that is, shortest) path to a destination Unlike OSPF, which was developed and standardized by the Internet Engineering Task Force (IETF),Protocol definition 1 the system of rules and acceptable behaviour used at official ceremonies and occasions 2 a Learn moreHTTP stands for Hyper Text Transfer Protocol WWW is about communication between web clients and servers Communication between client computers and web servers is done by sending HTTP Requests and receiving HTTP Responses




Routing Protocols Wiznet



Introduction To Is Is Network Direction
Today, the protocol remains one of the primary means of using the Internet How does HTTP work?



Is Is Intermediate System To Intermediate System Rick Graziani Cabrillo College Fall Ppt Download
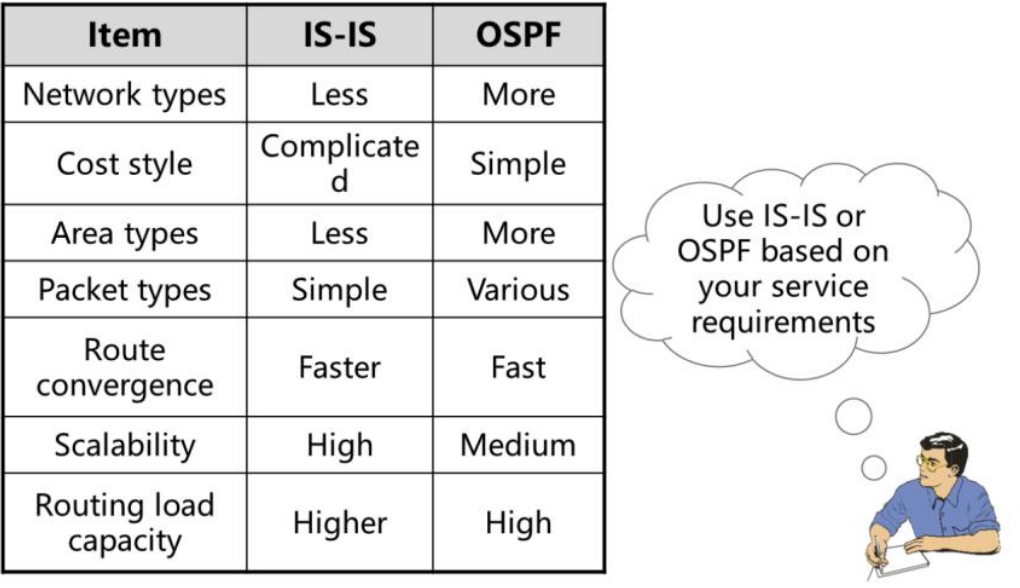



Why Do Many Isps Still Use The Is Is Instead Of The Ospf



Ip Routing Isis Configuration Guide Is Is Overview And Basic Configuration Cisco Asr 1000 Series Aggregation Services Routers Cisco



Your Session Is About To Expire Continue Session Your Session Has Expired Please Login To Vmware Docs Again Hello Vmware Logo Docs All Book Filter By All Book En Englishdeutschfrancaisespanol日本語한국어简体中文繁體中文russkijitaliano



Types Of Routing Protocols 3 1 4 Cisco Networking Academy S Introduction To Routing Dynamically Cisco Press




The Complete Is Is Routing Protocol Hannes Gredler Springer



Why Do Many Isps Still Use The Is Is Instead Of The Ospf




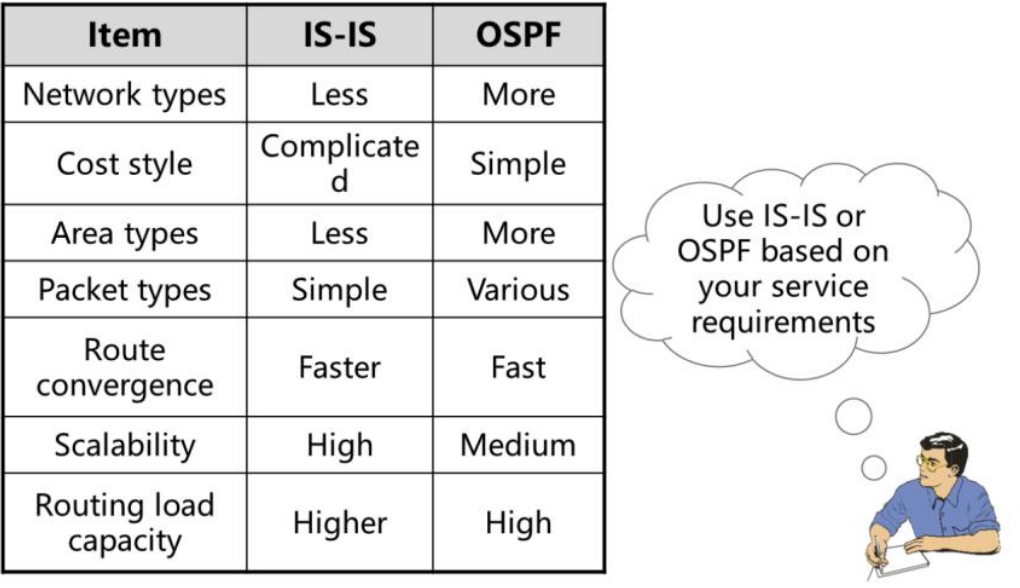
Ospf Vs Isis
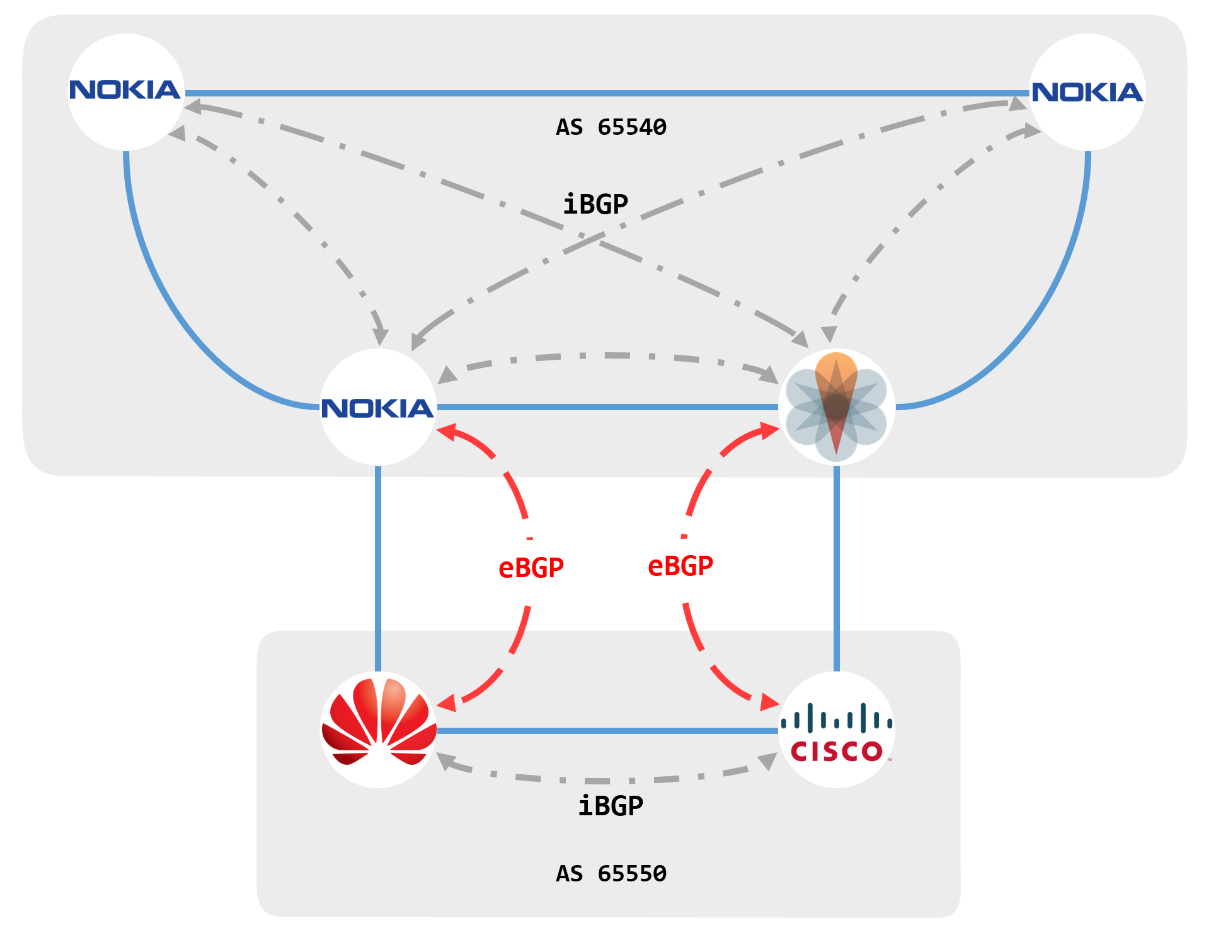



Bgp Configuration In Nokia Cisco Juniper And Huawei Part 1 Routecloud Indonesia Blog



Example Configuring Backup Selection Policy For Is Is Protocol Is Is User Guide Juniper Networks Techlibrary



Routing Protocols
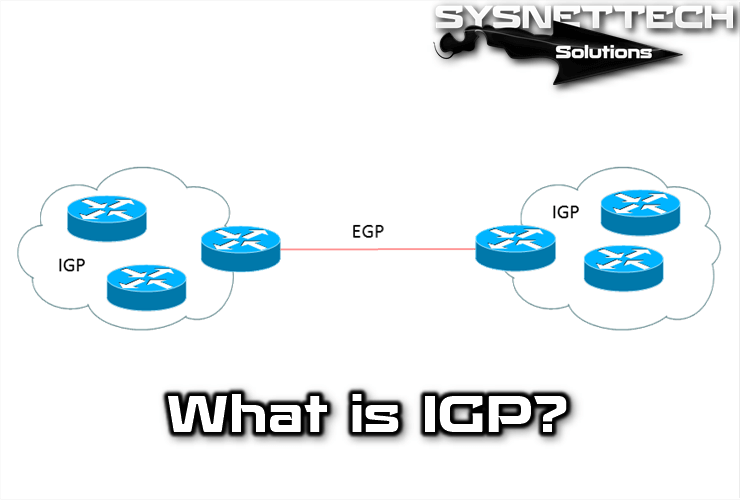



What Is Igp Protocol Sysnettech Solutions



What Is Enhanced Interior Gateway Routing Protocol Eigrp




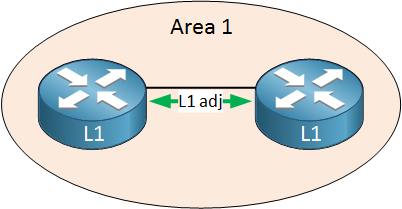
Is Is Adjacency Ipcisco



The Complete Is Is Routing Protocol Computer Science Books Amazon Com




Pdf Overview Of The Iso Is Is Intra Domain Routing Protocol



Is Is Tree



Why Do Many Isps Still Use The Is Is Protocol Instead Of The Ospf Protocol Huawei Enterprise Support Community



Routing Protocol Network Encyclopedia



The Complete Is Is Routing Protocol Computer Science Books Amazon Com



Intermediate System Intermediate System Is Is




Ospf Vs Isis



Introduction To Is Is Network Direction



Introduction To Is Is Network Direction



Intermediate System Intermediate System Is Is Protocol Octa Networks



Isis Training And Junos Configuration Inetzero Inetzero
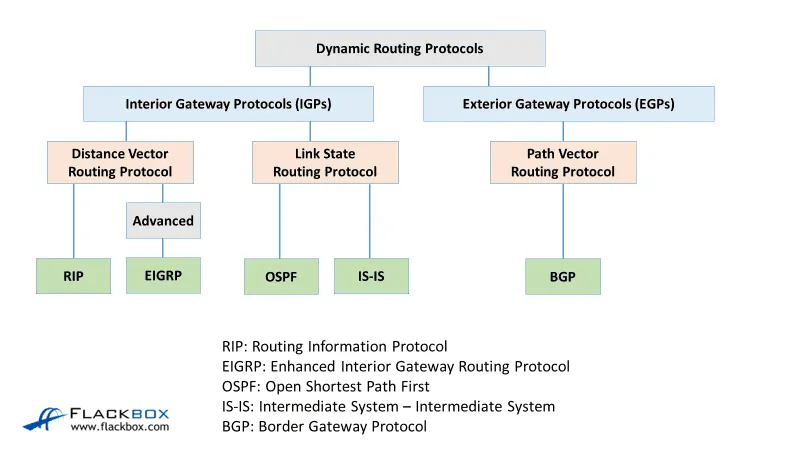



Cisco Routing Protocol Types Tutorial Flackbox




Atm And Multiprotocol Label Switching Mpls By Behzad



Configuring Is Is Protocol Overview Of Osi Protocols And Is Is Routing Cisco Press



Intermediate System Intermediate System Is Is Protocol Octa Networks



Ijesit Com




Episode 14 Digging Deep Into The Is Is Routing Protocol Network Collective




Cisco Routers Integrated Is Is Youtube



Cisco Ios Xr Complete Getting Started Examples Guide Part 2 2 Networkgeekstuff



Nokia Is Is Routing Protocol Exam Nokia
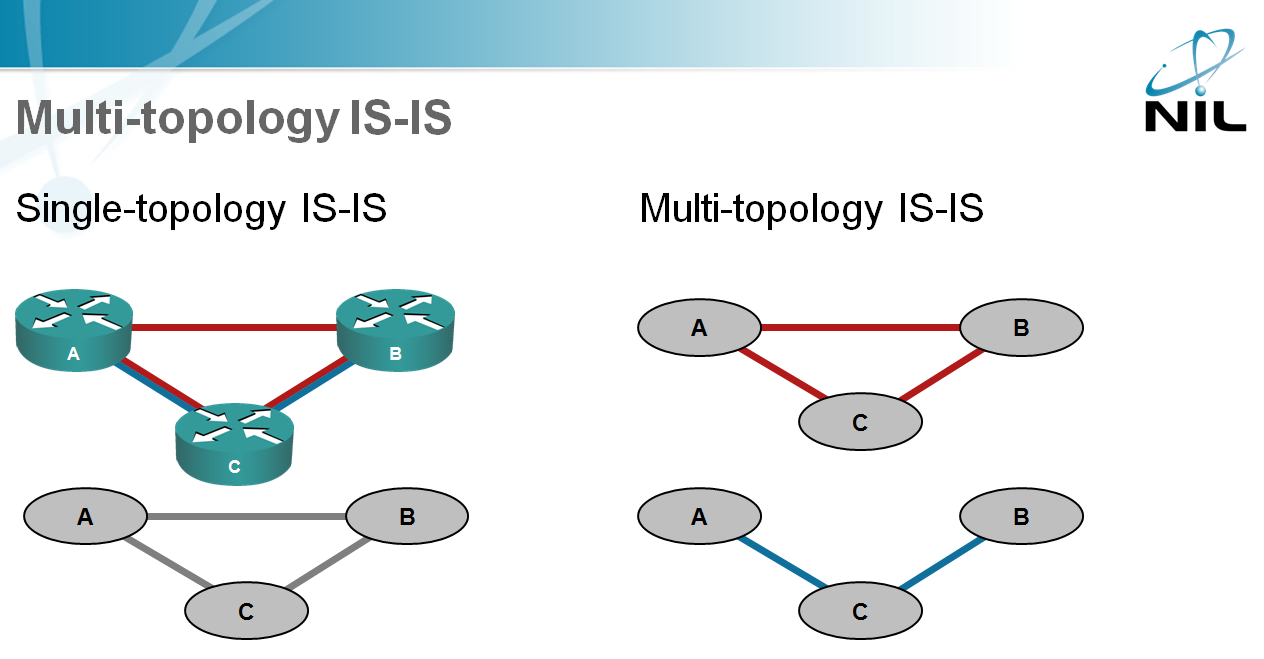



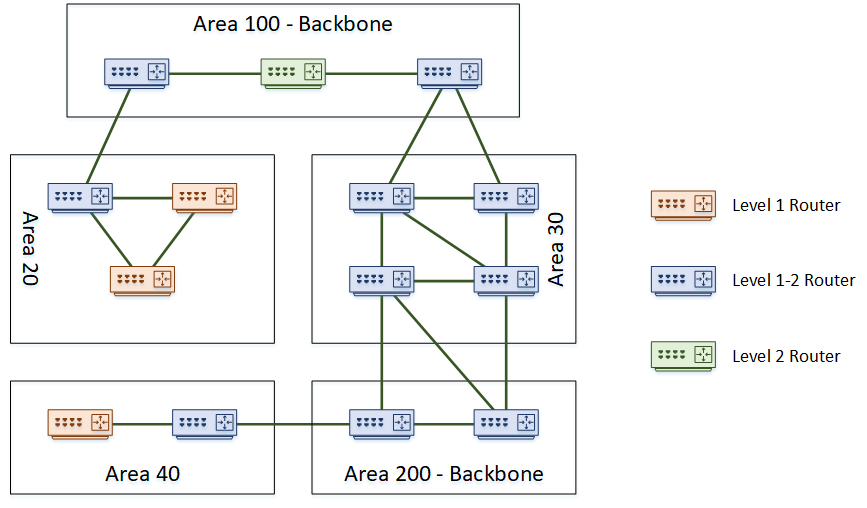
Multi Topology Is Is Ipspace Net Blog



Is Is Routing Protocol



Isis Dis Election Labnario



Isis Training And Junos Configuration Inetzero Inetzero




Is Is Hardcore Punk Garage Punk Hardcore Punk



Ip Routing Bgp Configuration Guide Cisco Ios Xe Gibraltar 16 12 X Configuring Multiprotocol Bgp Mp Bgp Support For Clns Cisco Ios Xe 16 Cisco



Is Is Protocol Adjacency
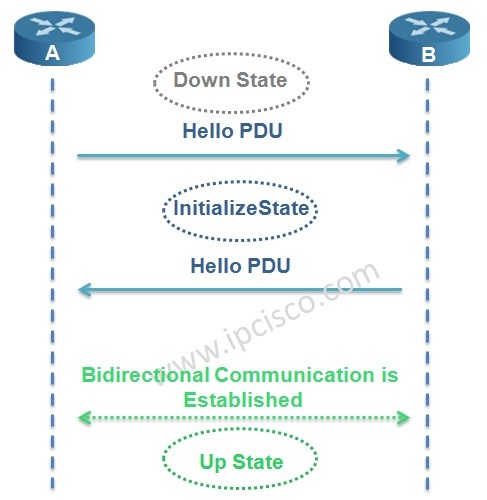



Is Is Adjacency Ipcisco



Eigrp Vs Ospf What S The Difference Fs Community




Intermediate System To Intermediate System Is Is Routing Protocol Fundamentals Youtube




A Quick Difference Ospf Vs Is Is Dynamic Routing Protocol



Is Is Protocol Adjacency



Introduction To Is Is




Is Is Routing Protocol Study Notes Part 1 Network Walks Academy



Verifying The Is Is Protocol Is Is User Guide Juniper Networks Techlibrary



Cisco Ios Xr Routing Fundamentals Of Ospf Isis And Bgp Intense School



Introduction To Is Is




What Is Ospf Protocol Ospf Basics And Overview Networkel



Isis Training And Junos Configuration Inetzero Inetzero
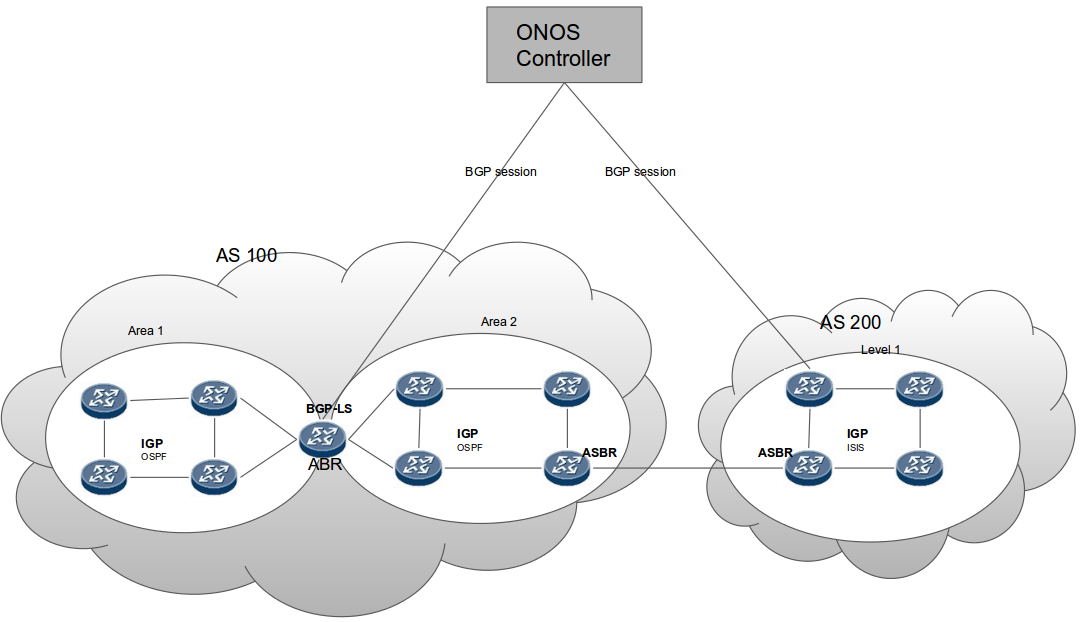



Bgp Protocol With Link State Distribution Onos Wiki



Introduction To Is Is



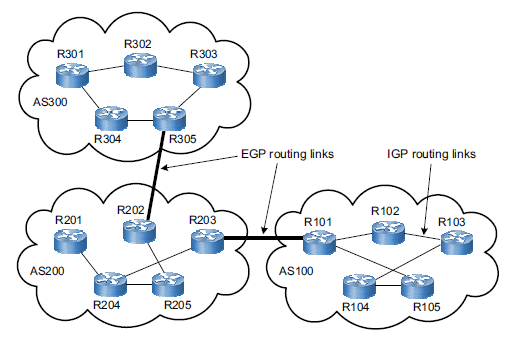
Exterior Gateway Protocols Egp And Bgpv4 Chapter 10 Isp Connectivity With Bgpv4 An Exterior Gateway Path Vector Routing Protocol For Interdomain Routing Integrated Cisco And Unix Network Architectures Networking Etutorials Org




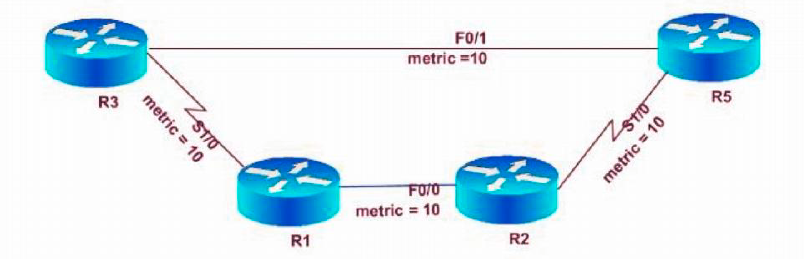
Isis Narrow And Wide Metrics Mom Network Engineer Juniper Ambassador



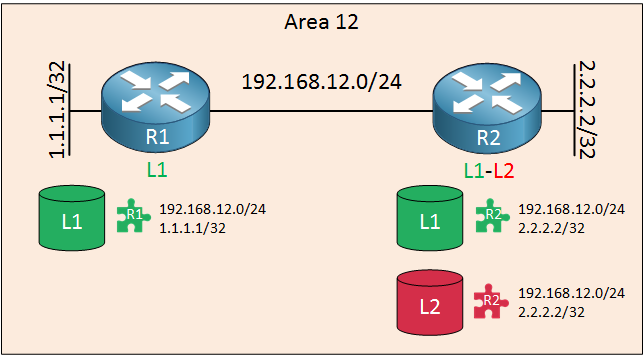
1




How Does Is Is Routing Protocol Work Step By Step Explaination




Seamless Suffering Routingcraft Net



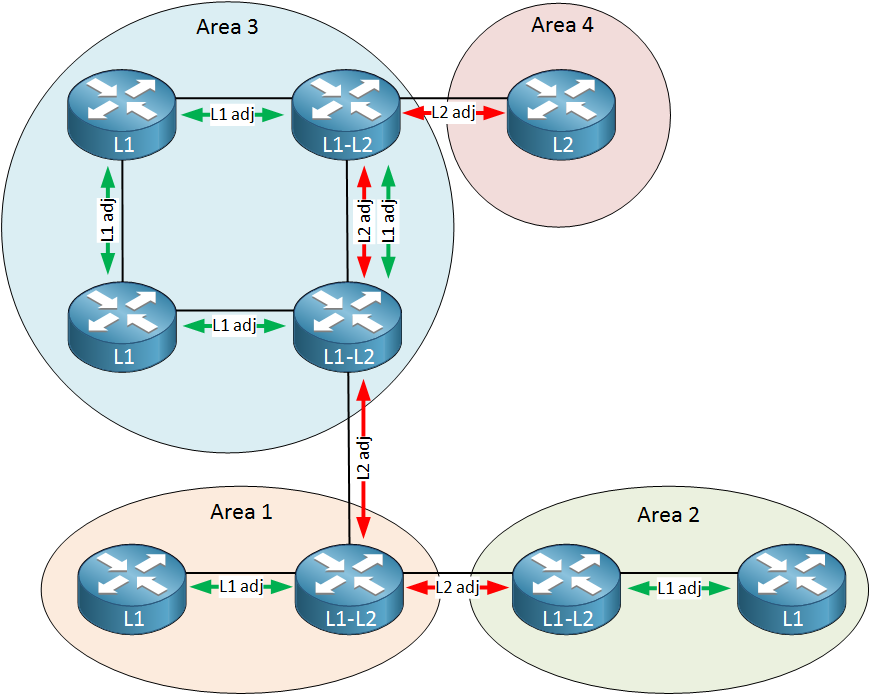
1




Your Session Is About To Expire Continue Session Your Session Has Expired Please Login To Vmware Docs Again Hello Vmware Logo Docs All Book Filter By All Book En Englishdeutschfrancaisespanol日本語한국어简体中文繁體中文russkijitaliano



Isis Vs Ospf




1 Bgp Protocol Illustration Download Scientific Diagram



Open Shortest Path First Ospf Set 2 Geeksforgeeks



Vpn And Connectivity Services



Is Is Adjacency Ipcisco
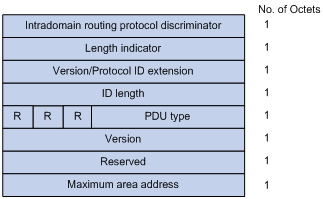



Is Is Pdu Format



Routing V S Routed Protocols In Computer Network Geeksforgeeks




Ccnp Route 300 101 Part 3 5 Evaluate Routing Protocol Types Ethernuno



Isis Training And Junos Configuration Inetzero Inetzero




Isis Cheat Sheet Will Help You On Isis Protocol Network Solution



Rip Vs Ospf What Is The Difference Fs Community
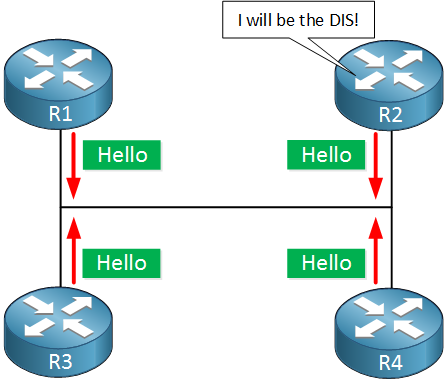



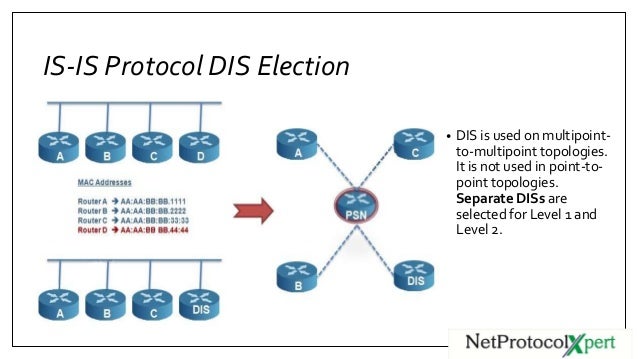
Is Is Dis And Pseudonode



Foundation Topics Chapter 9 Fundamentals Of The Integrated Is Is Protocol Part Iv Is Is Ccnp Bsci Official Exam Certification Guide Certification Etutorials Org




Dr Versus Dis What S The Diff Rule 11 Reader



Isis Training And Junos Configuration Inetzero Inetzero



Introduction To Is Is Network Direction




Is Is Control Messages Me60 V800r010c10spc500 Feature Description Wan Access 01 Huawei
コメント
コメントを投稿